Beyond Signatures: How Machine Learning and Autonomous Agents Are Redefining Intrusion Detection
This article explores the transition from signature-based intrusion detection to context-aware systems using machine learning and agentic AI, highlighting SnortML and autonomous decision-making.
Introduction
For decades, intrusion detection systems (IDS) have relied on signature-based methods to identify threats. These systems work by comparing network traffic against a database of known attack patterns—a straightforward but increasingly brittle approach. However, the rise of machine learning, exemplified by tools like SnortML, and the emergence of agentic AI are fundamentally changing the landscape. The central question is no longer “does this match a known pattern?” but rather “does this actually make sense in context?” This shift from static matching to dynamic reasoning promises more robust and adaptive security postures.
The Limitations of Signature-Based Detection
Traditional signature-based IDS excel at recognizing known threats—malware payloads, exploit code, or command-and-control patterns that have been cataloged. Yet this strength is also its weakness. Zero-day attacks, polymorphic malware, and subtle lateral movements often evade detection because they do not align with any precomputed signature. The system is, by design, reactive and brittle. In large, dynamic networks, maintaining an up-to-date signature database becomes a logistical burden, and false positives can overwhelm analysts.
Machine Learning: Adding Context to Detection
Machine learning (ML) offers a way to break free from the signature paradigm. Instead of memorizing attack patterns, ML models learn what “normal” network behavior looks like. Anomalies are flagged not because they match a known bad pattern, but because they deviate from expected baselines. This enables detection of novel threats, insider misuse, and sophisticated attacks that signature-based systems miss.
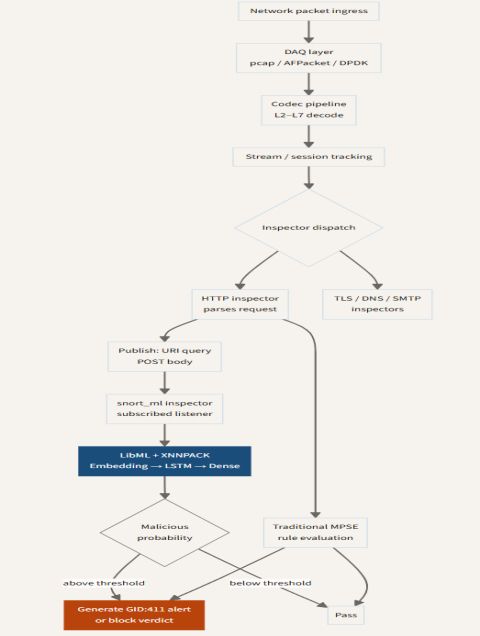
SnortML: Bringing ML to the Snort Ecosystem
SnortML is a notable implementation that extends the popular open-source IDS Snort with machine learning capabilities. By integrating models directly into the packet processing pipeline, SnortML allows analysts to apply custom ML classifiers to network flows. For example, a model might learn to distinguish between benign web traffic and a data exfiltration attempt based on packet timing, payload entropy, or connection patterns. This contextual analysis reduces reliance on static signatures and enables real-time adaptation to evolving threats.
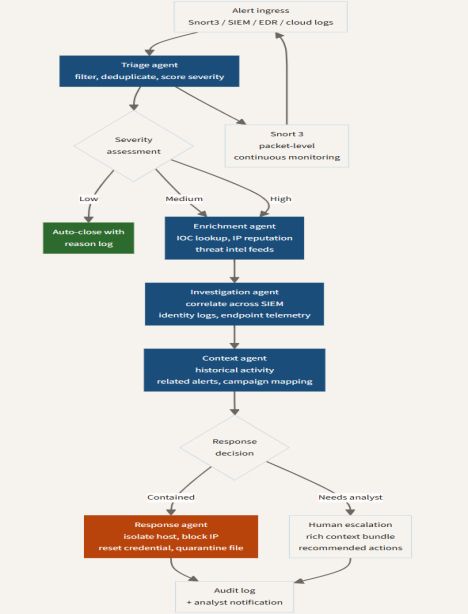
Agentic AI: Autonomous Decision-Making in IDS
While machine learning improves detection fidelity, agentic AI takes the next logical step: giving the sensor the ability to act autonomously. An agentic IDS can not only detect an anomaly but also initiate response actions—such as blocking a suspicious IP, quarantining a host, or altering firewall rules—without waiting for human approval. These agents operate by reasoning about context, evaluating risk, and executing policies defined by security teams.
How Autonomous Agents Differ from Pure ML
Pure ML models output a prediction (e.g., “this is 95% likely to be an attack”). Agentic systems, by contrast, possess a feedback loop: they observe, decide, act, and then learn from the outcome. For instance, if an agent blocks a connection and later determines that the block caused a false positive, it can adjust its thresholds or notify an analyst. This self-improving cycle makes agentic AI particularly suited for environments where threat patterns shift rapidly.
Evolving Architecture: From Monolithic to Distributed Intelligence
The integration of ML and agentic AI is also reshaping the architecture of intrusion detection. Traditional IDS are often centralized: all traffic flows to a single appliance for analysis. Modern architectures distribute intelligence to network edges, endpoints, and cloud gateways. Sensors running lightweight ML models and small agentic loops can process data locally, reducing latency and bandwidth use. Centralized systems then correlate alerts from many distributed sensors, providing a global view.
A Hybrid Approach
The most effective deployments combine signature-based, ML, and agentic techniques. Signatures handle the “known knowns” efficiently. ML models catch “unknown knowns”—anomalies that deviate from learned norms. Agentic AI manages “unknown unknowns” by adapting strategies in near-real-time. This layered defense strengthens overall resilience.
Challenges and Considerations
Transitioning to ML and agentic detection is not without obstacles. ML models require careful training on representative data to avoid bias; otherwise, they generate excessive false positives or miss subtle attacks. Agentic systems raise concerns about accountability—who is responsible if an autonomous agent makes a harmful decision? Additionally, adversarial attacks can poison training data or evade model detection. Security teams must invest in robust testing, explainability, and human oversight.
Future Outlook
As network traffic volumes grow and attacks become more sophisticated, the sensor that can think—by applying context, learning from experience, and acting autonomously—will become indispensable. SnortML and similar projects exemplify this trend, but they are just the beginning. The future of intrusion detection lies in continuous, context-aware reasoning that evolves alongside the threat landscape.
In summary, the shift from “does it match?” to “does it make sense?” represents a fundamental rethinking of security monitoring. By embracing machine learning and autonomous agents, organizations can move from reactive defense to proactive, adaptive protection.